Captcha technology– initially an acronym for “Completely Automated Public Turing test to tell Computers and Humans Apart” – is broadly used to keep bots from getting to frames on sites. It works by exploiting a human’s better capacity than perceiving designs in pictures.
Now, scientists from the Georgia Tech Institute have developed a new login authentication approach that could improve the security of current biometric techniques that rely on video or images of users’ faces. The technique named Real-Time Captcha utilizes an interesting test that is simple for people — yet troublesome for assailants who might utilize machine learning and picture-age programming to parody true blue clients.
The technique requires users to investigate their cell phone’s camera while noting an arbitrarily chosen inquiry that shows up inside a Captcha on the screens of the gadgets. The response must be given within a restricted timeframe that is too short for computerized reasoning or machine learning projects to react.
The Captcha would supplement picture and sound-based verification strategies that can be ridiculed by aggressors who might have the capacity to discover and alter pictures, video, and the sound of clients — or take them from cell phones.
Erkam Uzun, a graduate research assistant in Georgia Tech’s School of Computer Science, said, “The attackers now know what to expect with authentication that asks them to smile or blink, so they can produce a blinking model or smiling face in real time relatively easily. We are making the challenge harder by sending users unpredictable requests and limiting the response time to rule out machine interaction.”
Wenke Lee, a professor in Georgia Tech’s School of Computer Science, said, “In the cat-and-mouse game of cybersecurity, that biometrics can be spoofed or stolen, which will force companies to find better approaches.”
“If the attacker knows that authentication is based on recognizing a face, they can use an algorithm to synthesize a fake image to impersonate the real user,” Lee said. “But by presenting a randomly selected challenge embedded in a Captcha image, we can prevent the attacker from knowing what to expect. The security of our system comes from a challenge that is easy for a human, but difficult for a machine.”
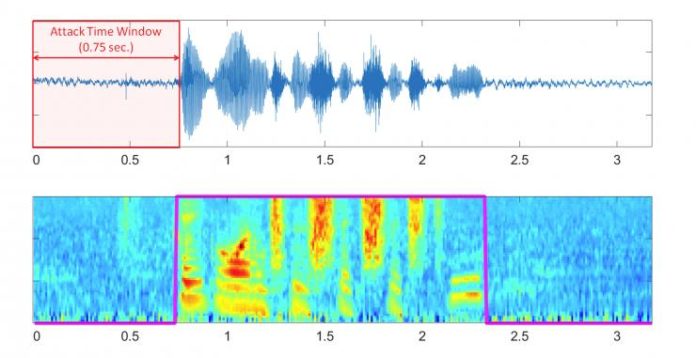
During the experiments with 30 subjects, humans could successfully respond to the challenges in one second or less. On the other hand, the machines required between six and ten seconds to decode the question.
The new approach would require login requests to finish four tests: effective acknowledgment of a test question from inside a Captcha, reaction inside a thin time window that no one but people can meet, and fruitful matches to the genuine client’s pre-recorded picture and voice.
To improve authentication, scientists studied image spoofing software and tried to open a new front in the battle against attackers. The approach moves the attackers’ task from producing a persuading video to breaking a Captcha.
Lee said, “For any security mechanism that we develop, we need to worry about the security of the mechanism first. Once you develop security technology, it becomes a target for the attackers, and that certainly applies to biometric technology.”
Journal Reference
- Erkam Uzun, Simon Pak Ho Chung, Irfan Essa and Wenke Lee, “rtCaptcha: A Real-Time CAPTCHA Based Liveness Detection System,” (Network and Distributed Systems Security (NDSS) Symposium 2018).