Current email arrangements utilize administer based strategies and analyze other elements of the message. Existing antivirus engines primarily use signature-based detection methods and therefore are insufficient for detecting new, unknown malicious emails.
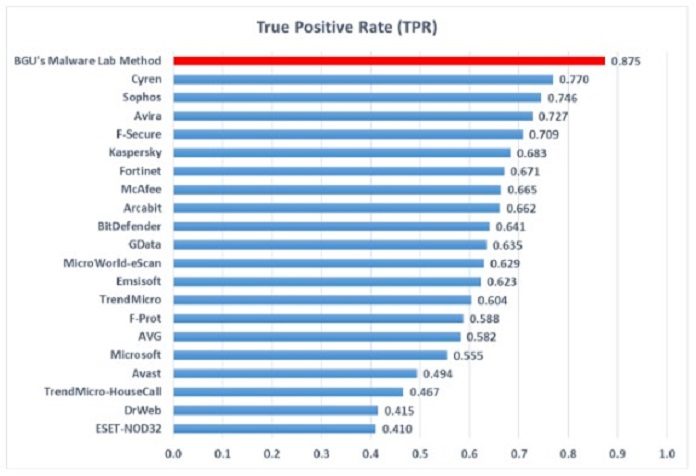
Specialists at the Ben-Gurion University of the Negev (BGU) Malware Lab have built up another strategy for distinguishing malicious emails that is more viable than the best 60 antivirus engines available.
The new method dubbed Email-Sec-360° leverages 100 general descriptive features extracted from all e-mail components, including header, body, and attachments, to detect a malicious message. Created by the Ph.D. student and analyst Aviad Cohen, the strategy is based on machine learning standards and works without web get to, making it a valuable answer for the two people and organizations.
To work out their location display, the scientists utilized 33,142 messages (12,835 malignant and 20,307 generous), which they gathered in the vicinity of 2013 and 2016, the discharge noted. After testing, analysts found that their technique beat the following best antivirus engine by 13 percent.
Dr. Nir Nissim said, “In future work, we are interested in extending our research and integrating analysis of attachments, such as PDFs and Microsoft Office documents within Email-Sec-360° since these are often used by hackers to get users to open and propagate viruses and malware.”
“In addition, the system would assist in collecting benign and malicious e-mails for research purposes which, due to privacy issues, is currently a very difficult task for researchers in this arena.”
The research was published in the exclusive scientific journal Expert Systems with Applications.